Women as the target
In an exploratory study of women and online verbal abuse in India by the Internet Democracy Project (IDP), titled ‘Don’t let it Stand!’, it was found that very often threats were simply because the person was a woman. The study systematically considers in-depth, the ways in which women face and counter gender-based abuse in online spaces. It is this study that highlighted instances such as the tweet about a milk carton referred to earlier.
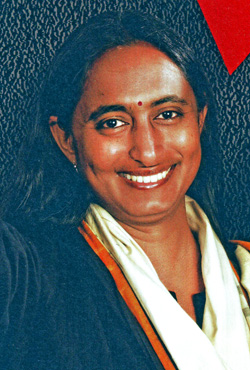
The IDP study cites the example of Sagarika noting that while her husband, Rajdeep Sardesai, also a well-known journalist, gets viciously attacked on Twitter for his views, the vitriol that he has to face is not of a sexually violent nature.
Another person quoted in the IDP study says the real problem is when “they do not talk about my thought process, but about my appearance”.
Advocate and founder-member of Mumbai-based Technology Law Forum, N S Nappinai says it’s almost as if the easiest way to threaten a woman is to tell her she will be stripped or raped. “And it spreads easily on the Internet.”
Chinmayi identifies this as “playing on the collective, regressive belief system that has been established in India that a woman who is sexually assaulted in any degree will be the one facing shame and not the aggressor.”
And all this is done knowing that unlike on the streets, where there is a face to the abuser, in the online space, one can get away without revealing one’s identity. Sagarika says, “It’s easy to attack women on social media as you can hide under the cover of anonymity.”
While it may not be common or easy to call someone a ‘slut’ or threaten to gang rape her in the real world, there is the feeling of being able to express these sentiments freely, without fear, on the Internet.
In IDP’s study, Mumbai-based blogger Trishna is quoted saying, “There’s a mob mentality which is as real as on the street. Gentle people who on a road would not get down and hammer people, given the chance to do it virtually, they [won’t think twice]”. She adds, “…This virtual interaction…I think a lot of people misuse the Internet because anonymity gives you so much freedom.”
The power of anonymity
So what does one do when faced with such threats and abuse online? Those like Sagarika, Chinmayi and Kavita have gone to the police and lodged a complaint.
In Chinmayi’s case, at least one person was arrested for harassing her online. However, Sagarika says that since a number of these Twitter handles are anonymous, the police do not seem to be able to track them down, which was the case with her. A similar problem in Kavita’s case because of which the police are closing her complaint, she says.
This is a common problem faced by many when reporting such cases.
Says D Roopa, Superintendent of Police, CID-Cyber Crime, Karnataka, “Very often it is difficult because even IP addresses are masked. The challenge with cyber-crime is that it is transnational. There are so many tools available to remain anonymous.”
She gives the example of a Bangalore woman who filed a complaint in 2010 after she found morphed photographs of herself doing the rounds on more than 3000 websites. Despite a court order to get these sites blocked, CERT-In or Computer Emergency Response Team-India, the national nodal agency for responding to computer security incidents as and when they occur, has not done so. The only positive in this case is that the accused, found to be her ex-boyfriend, has been charge-sheeted. However, the victim continues to live with the fact that the obscene photos are still in the public domain.
Roopa explains that since companies like Facebook and Twitter are headquartered abroad, “they take about three months to reply about the identity of a person. When it comes to deleting content, that gets done quickly. But they take time to give information about who posted a photo or comment.”
Take the case of Mumbai-based finance professional, Nidhi (name changed to protect identity) who has been battling a cyber crime case for more than six years now. In 2007, Nidhi filed a sexual harassment case against the partner in the organization she worked in. When the accused was arrested, a popular tabloid in the city reported the case, revealing details about her identity. The online version of this particular article received several slanderous and vulgar comments about her which failed the moderation, because of which she filed a complaint with the cyber crime cell of the Mumbai police. Subsequently, several other websites were found to be carrying slanderous comments about her, many even referring to her as a ‘dance bar girl’, ‘legal terrorist’ and a ‘prostitute’. She has since written to Google requesting them to remove the links to some of these websites. “Google advises action against the hosting sites to curb this cyber slander,” she says.
In June 2012, Nidhi filed an RTI application requesting information from the police about what action has been taken on her complaint against the websites. “I have to use an RTI to find out about the status of my own complaint”. A month later, the police responded to her RTI application saying that letters had been sent to Google, Nabble, 498A[dot]org but no response had been received. It also stated that a NC (non-cognizable) was filed in September 2010 and was closed as a civil case. “They never even informed me when they closed the complaint and the signature on the NC is not mine,” she says.
On 3 November 2012, the Chief Metropolitan Court passed an order directing CERT-In and Google to delete a set of defamatory blogs against her. The Police is empowered to obtain such an order from the Court as per section 69A of the IT Act, she says. This section refers to the power to issue directions for blocking public access of any information through any computer resource. Even a month from that date, Nidhi says some of the defamatory comments remained online. She again filed RTI applications, one seeking a copy of the court order from the Police, and another seeking the status of implementation of the said order by CERT-In. It was only on 28 December 2012 that the court order was implemented by the Department of Electronics and IT, she discovered.